Risk Management Enterprise Can Be Fun For Anyone
Table of ContentsEverything about Risk Management EnterpriseRisk Management Enterprise Can Be Fun For EveryoneA Biased View of Risk Management EnterpriseGet This Report about Risk Management EnterpriseFascination About Risk Management EnterpriseThe smart Trick of Risk Management Enterprise That Nobody is Talking AboutExcitement About Risk Management Enterprise
Real-Time Threat Evaluations and Reduction in this software permit companies to constantly check and assess threats as they advance. When risks are determined, the software program promotes prompt mitigation activities.
KRIs fix the problem of irregular or vague risk evaluation. They resolve the challenge of ongoing threat administration by offering devices to check risks constantly. KRIs improve protection threat oversight, making sure that potential risks are determined and managed successfully. The task of risk monitoring must not be a difficulty. Consequently, companies have to depend on a superior and advanced threat administration software program.
6 Simple Techniques For Risk Management Enterprise
IT take the chance of management is a part of business danger management (ERM), designed to bring IT run the risk of in line with an organization's risk cravings. IT risk monitoring (ITRM) includes the policies, procedures and modern technology essential to decrease risks and vulnerabilities, while maintaining compliance with appropriate regulative demands. Furthermore, ITRM seeks to limit the consequences of devastating events, such as safety and security breaches.
Veronica Rose, ISACA board supervisor and an info systems auditor at Metropol Corp. The ISACA Threat IT structure lines up well with the COBIT 2019 framework, Rose stated.
Business Threat Monitoring Software Application Development: Advantages & Features, Cost. With technical developments, risks are constantly on the surge., companies browse through a continuously changing sea of risks.
Some Known Questions About Risk Management Enterprise.
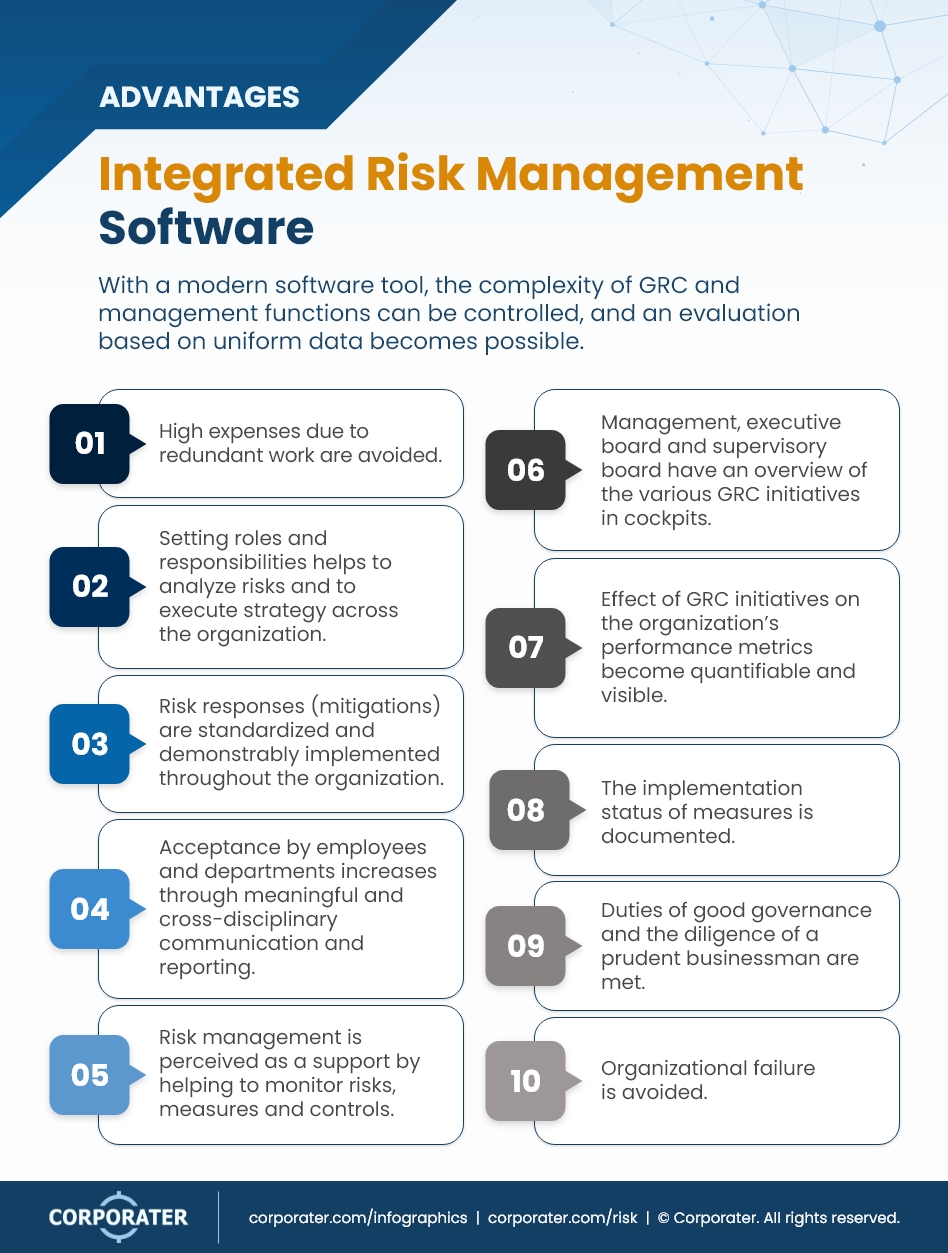
In this blog, we will dive into the world of ERM software program, discovering what it is, its benefits, features, etc so that you can construct one for your organization. Venture Risk Administration (ERM) software program is the application program for preparation, routing, arranging, and controlling organization tasks and enhancing danger management processes.
With ERM, companies can make informative decisions to enhance the general durability of the business. Committed ERM systems are important for businesses that frequently deal with substantial quantities of sensitive details and numerous stakeholders to accept calculated decisions.
: It is stressful for any kind of enterprise to undergo a comprehensive audit. It can be prevented by using the ERM software system. This system automates policy conformity management to maintain the organization safe and secure and certified. Besides that, it additionally logs and classifies all the files in the system making it much easier for auditors to examine processes a lot quicker.
Top Guidelines Of Risk Management Enterprise
You can also link existing software systems to the ERM using APIs or by including information by hand. Organizations can utilize ERM to review threats based upon their potential influence for better risk administration and mitigation.: Adding this attribute permits users to get real-time notices on their gadgets about any threat that could take place and its impact.

Rather, the software program enables them to set limits for various procedures and send out push alerts in situation of feasible threats.: By integrating information visualization and reporting in the customized ERM software, organizations can acquire clear understandings about threat fads and performance.: It is mandatory for organizations to comply with industry conformity and regulatory criteria.
These platforms make it possible for firms to carry out best-practice danger management procedures that align with industry requirements, providing a powerful, technology-driven method to recognizing, analyzing, and mitigating threats. This blog site checks out the advantages of computerized threat management devices, the locations of threat management they can automate, and the worth they offer a company.
Excitement About Risk Management Enterprise
Groups can establish forms with the relevant areas and quickly develop different forms for various risk types. These threat analysis kinds can be flowed for completion via automated operations that send notifications to the relevant team to complete the kinds online. If types are not completed by the deadline, then chaser emails are instantly sent out by the system.
The control monitoring and control screening process can also be automated. Companies can utilize computerized workflows to send out routine control test notifications and team can go into the outcomes via on-line forms. Controls can likewise be checked by the software application by establishing rules to send out alerts based upon control data go to website held in other systems and spreadsheets that is pulled right into the system by means of API assimilations.
Risk administration automation software program can additionally sustain with risk reporting for all degrees of the enterprise. Leaders can see records on threat direct exposure and control effectiveness with a variety of reporting results including static records, Power BI interactive reports, bowtie analysis, and Monte Carlo simulations. The ability to pull actual time reports at the touch of a button eliminates tough data manipulation jobs leaving danger groups with even more time to evaluate the information and encourage business on the very best program of action.
Organizations operating in competitive, fast-changing markets can't afford hold-ups or ineffectiveness in resolving prospective threats. Standard danger administration using manual spreadsheet-based procedures, while familiar, frequently lead to their explanation fragmented data, taxing reporting, and a boosted chance of human mistake.
Risk Management Enterprise - An Overview
This makes sure threat registers are always existing and aligned with organizational purposes. Compliance is an additional important vehicle driver for automating threat management. Criteria like ISO 31000, CPS 230 and COSO all provide assistance around danger management ideal techniques and control frameworks, and automated risk management tools are structured to straighten with these needs aiding companies to fulfill most typically made use of risk monitoring requirements.
Search for danger software platforms with a consents power structure to conveniently set up process for risk rise. This performance enables you to customize the view for each customer, so they only see the information relevant to them. See to it the ERM software uses customer monitoring so you can see who entered what data and when.
Choose a cloud-based platform to guarantee the system obtains normal updates from the supplier adding brand-new capability. Seek devices that use task danger administration capacities to manage your jobs and portfolios and the associated dangers. The advantages of embracing danger administration automation software program expand far beyond effectiveness. Companies that incorporate these services right into their ERM technique can expect a host of substantial and intangible.
Fascination About Risk Management Enterprise
While the situation for automation is engaging, executing a danger administration system is not without its difficulties. To overcome the difficulties of risk monitoring automation, organizations need to spend in data cleansing and governance to make sure a solid foundation for executing an automated system.
Automation in threat management encourages organizations to change their approach to run the risk of and construct a stronger foundation for the future (Risk Management Enterprise). The question is no much longer whether to automate danger administration, it's how soon you can begin. To see the Riskonnect at work,
The answer often exists in exactly how well threats are anticipated and managed. Job monitoring software application serves as the navigator in the tumultuous waters of project implementation, offering tools that determine and evaluate threats and devise strategies to alleviate them efficiently.